Analysis of the Curio Exploit
Learn how Curio was exploited, which resulted in a loss of approximately $16 million.
Youtube Video
Playing the video that you've selected below in an iframe

Ankr protocol a web3 infrastructure provider suffered a governance key compromise.
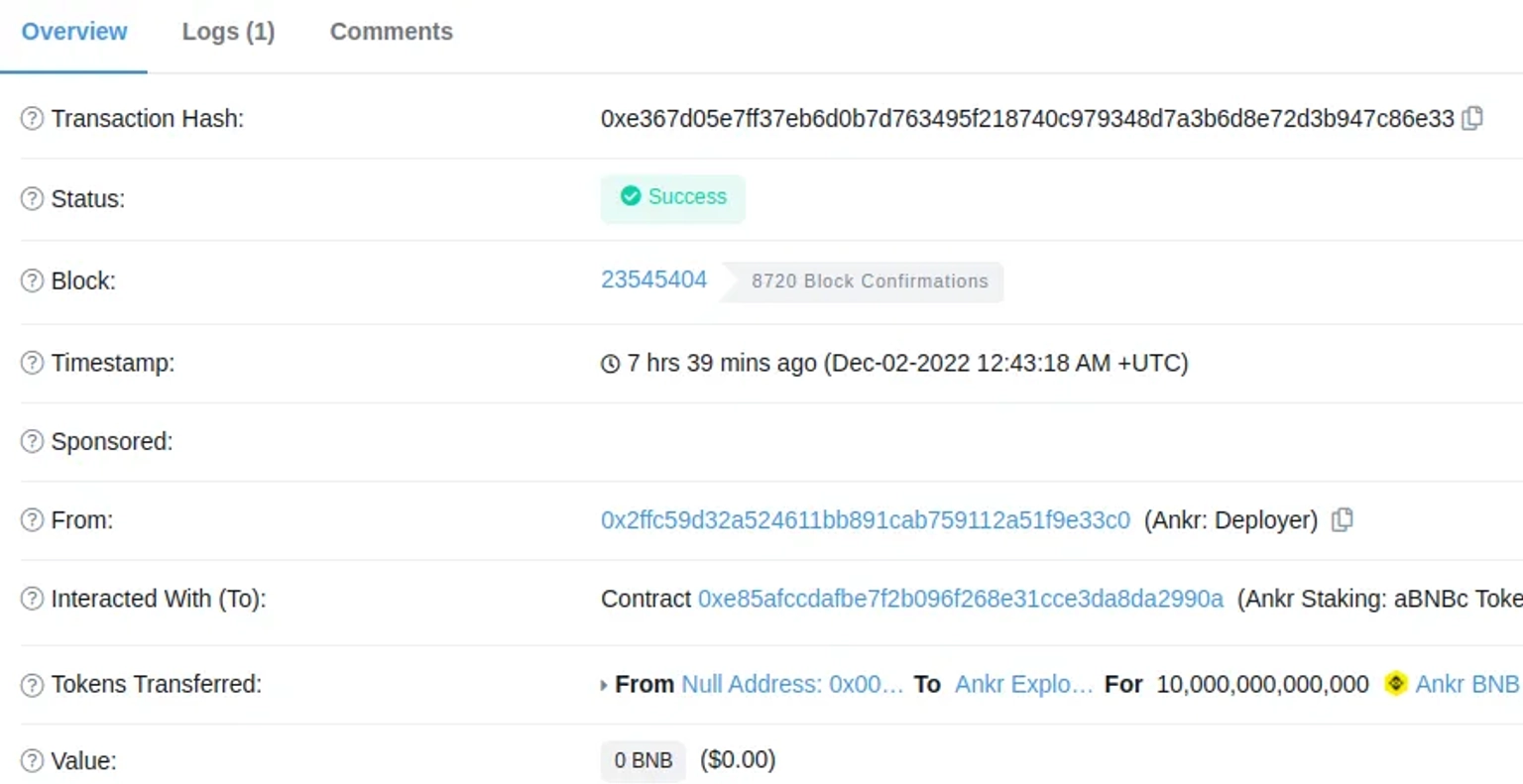
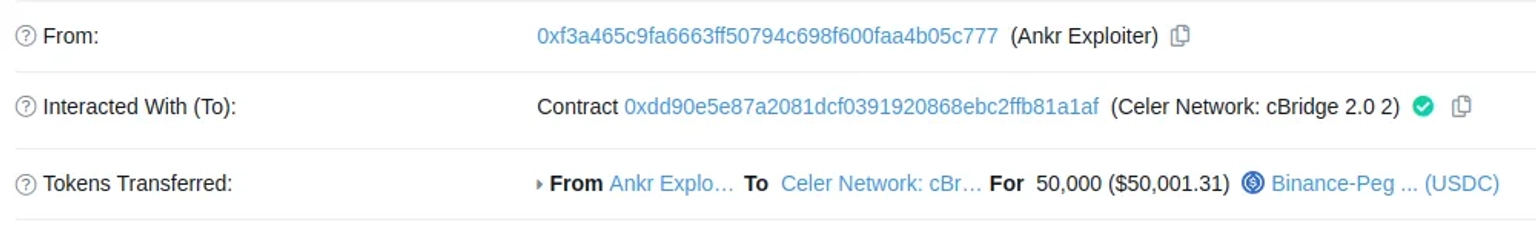
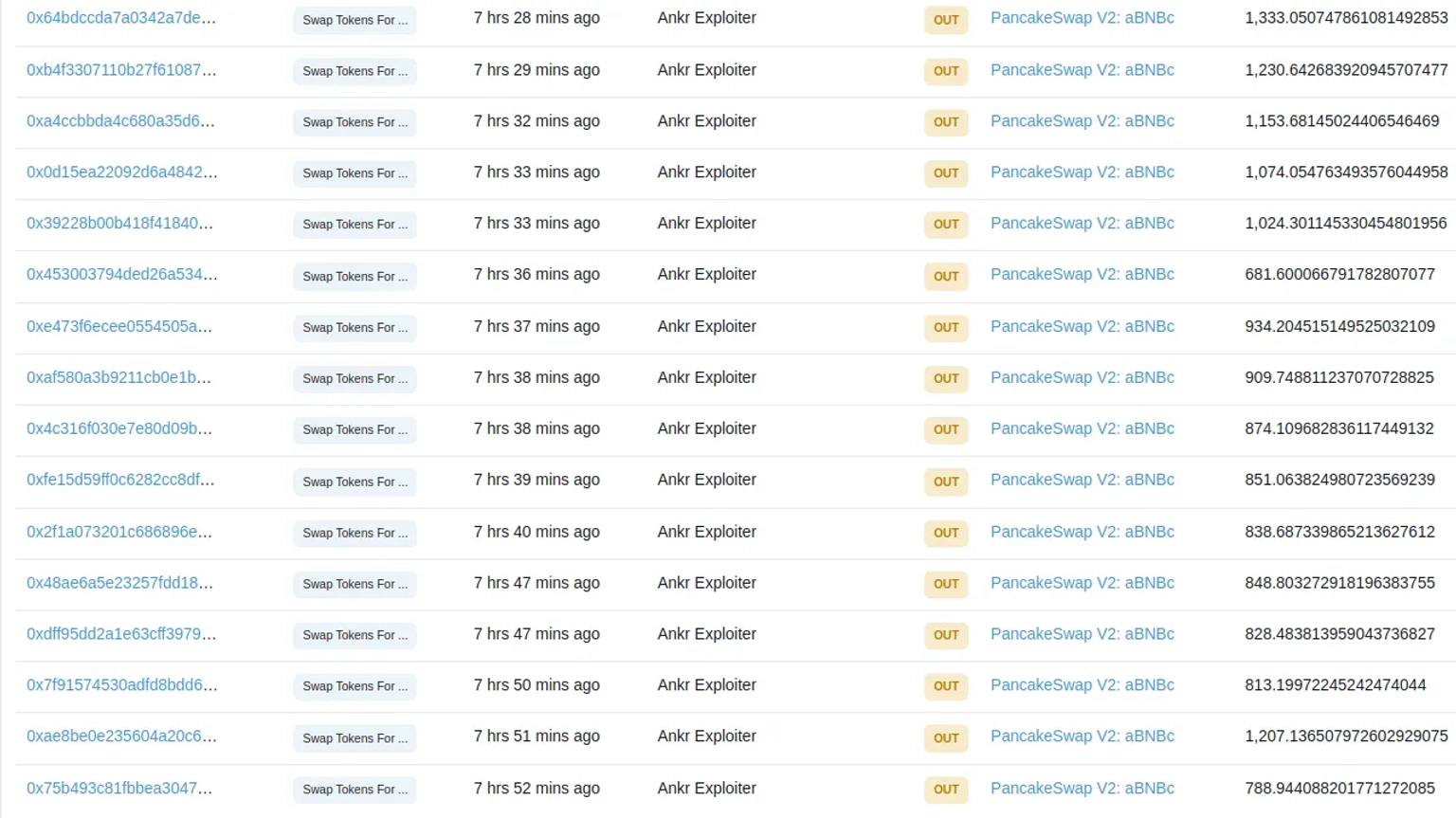
On December 02, 2022, the Ankr protocol on BNB chain suffered a governance key compromise, allowing an attacker to mint 10,000,000,000,000 $aBNBc tokens and drain the DEX pool, resulting in the loss of approximately $5 million.
Ankr is a decentralized Web3 infrastructure provider that helps developers, decentralized applications, and stakers interact easily with an array of blockchains.
The root cause of the vulnerability is due to the compromise of their governance key.
After the incident, the team issued a statement on Twitter mentioning that they were currently working with exchanges to immediately halt trading. The price of the $ANKR token plummeted and was last observed trading at $0.02168.
In addition, they stated that all the underlying assets on Ankr Staking were safe at this time, and all infrastructure services are unaffected. The team will be drafting a plan to compensating affected users.
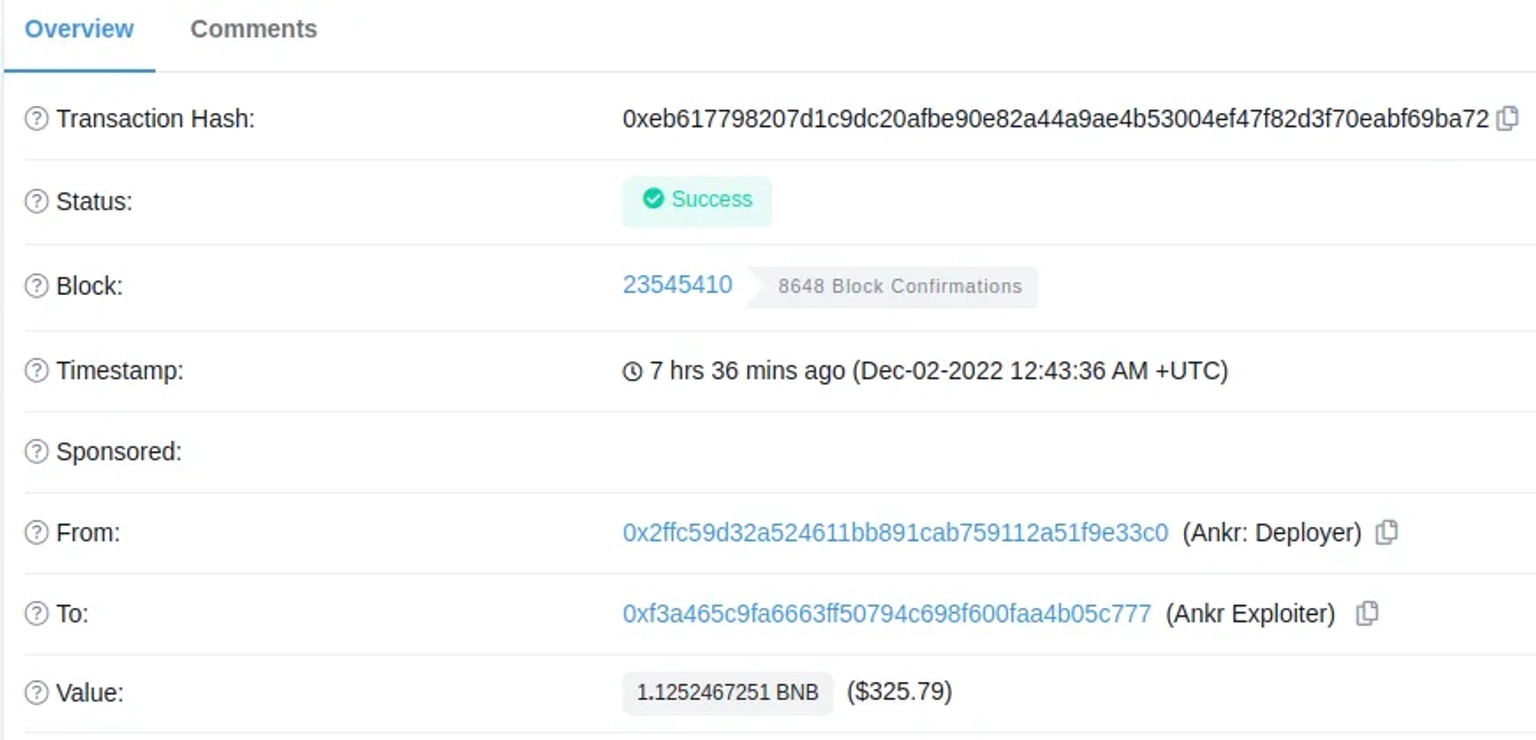
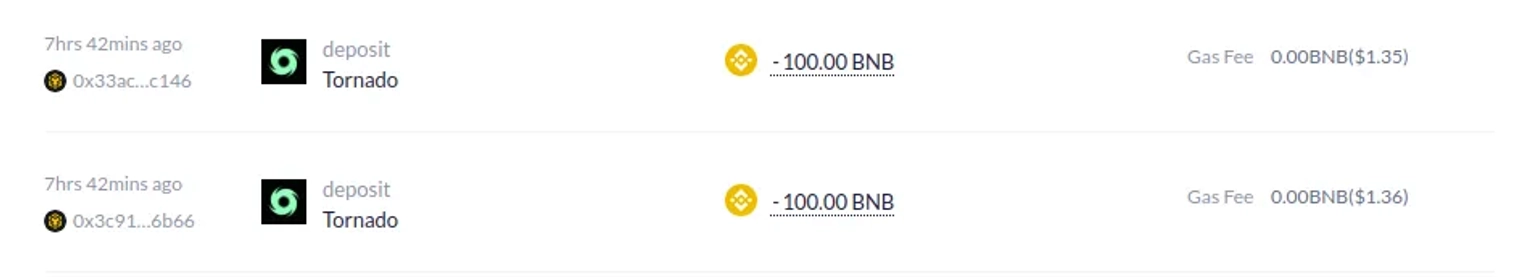
The exploiter deployed an attack contract, changed the upgradeable aBNBc contract to the malicious implementation, and then minted a massive amount of tokens for his wallet. This can either be caused by the compromise of the private key of the deployer during their migrations, or it could also potentially be an insider job where the attack was planned to coincide with the event.
Multisignature wallets and pause contract events are also industry standards for the majority of blockchain teams to mitigate against events of such nature to a greater extent.
Had Ankr partnered with Neptune Mutual to set up a dedicated coverage pool before the incident, the fallout might have been significantly mitigated. At Neptune Mutual, we understand the intricacies of the DeFi landscape, which is why we offer coverage to users who might face losses from vulnerabilities in smart contracts.
Our avant-garde parametric policies ensure that users are not mired in bureaucratic processes when proving their losses. Instead, they can readily claim their payouts and post an incident's confirmation and resolution through our rigorous incident resolution framework.
Our security team at Neptune Mutual can validate your platform for DNS and web-based security, smart contract reviews, as well as frontend and backend security. We can offer you a solution to scan your platform and safeguard your protocol for known and unknown vulnerabilities that have the potential to have catastrophic long-term effects. Contact us on social media if you are serious about security and have the budget, desire, and sense of responsibility to do so.
Reference Sources PeckShield, BlockSec