Analysis of the Curio Exploit
Learn how Curio was exploited, which resulted in a loss of approximately $16 million.
Youtube Video
Playing the video that you've selected below in an iframe
Roast Football suffered a unique attack, manipulation on the reward system to book a profit.
On December 05, 2022, Roast Football was a victim of an attack, in which the exploiter repeatedly swapped $RBF and $WBNB tokens by manipulating their reward system to book a profit of approximately 12 $BNB worth $3500.
The occurrence of this exploit is unique when compared to the other analyses that we have covered. The project's smart contract operation also relied on the block number and time stamp, which was eventually exploited by the attacker.
Roast Football $RBF is a BSC token, which according to the team, follows the roast beef model for the world's first soccer hot spot, as well as the lottery mechanism double economic model.
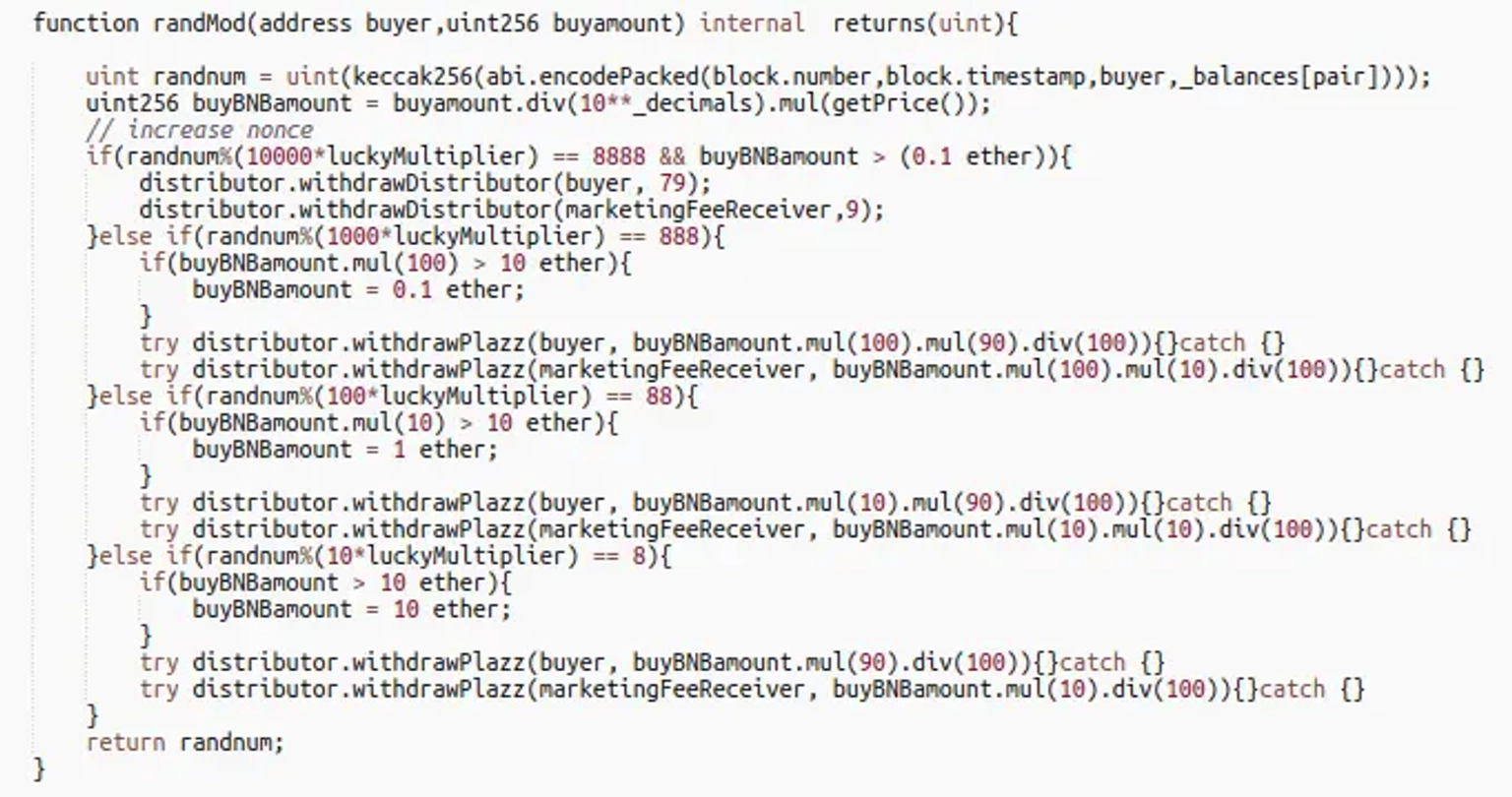
The vulnerability is caused by a weak pseudorandom number generator in the lottery function, which executes transactions only when the lottery is won.
The team has not released a post-mortem report detailing the incident.
There are many a potential issues with the implementation of this function. The use of block number, and time stamp in the generation of a random number can be exploited by an attacker who can predict these values. This would allow an attacker to manipulate the outcome of the random number generation, and gain an unfair advantage in the distribution of the funds.
The use of catch statement to ignore any errors in the transfer of funds may also hide potential issues with the transfer of funds.
The impact of this attack could have been significantly reduced if Roast Football had a dedicated cover pool in the Neptune Mutual marketplace. We have standard terms and conditions in place to provide coverage to various types of DeFi attacks, but we are also open to make exceptions in some cases.
Users who purchase our parametric cover policies do not need to provide loss evidence in order to receive payouts. Payouts can be claimed as soon as an incident like this is resolved through our governance system.
Additionally, auditing the smart contracts for vulnerabilities is insufficient due to the existence of varying attack vectors. Neptune Mutual's security team can also assess your preferred protocol for DNS and web-based security, smart contract evaluations, and frontend and backend security.