Understanding the XBridge Exploit
Learn how XBridge was exploited, resulting in a loss of assets worth approximately $1.44 million.
Youtube Video
Playing the video that you've selected below in an iframe

Learn how Sturdy Finance was exploited, resulting in a loss of funds worth 442 ETH.
On June 12, 2023, Sturdy Finance was exploited due to a smart contract vulnerability, which resulted in a loss of 442 ETH, worth approximately $775,332.
Sturdy enables yield farmers to get higher leverage for farming projects by supporting staked assets as collateral.
The root cause of the vulnerability is due to the well-known read-only reentrancy associated with Balancer, which led to the faulty price oracle to compute the cB-stETH-STABLE asset price.
Step 1:
We attempted to analyse the attack transactions executed by the exploiter.
Step 2:
The exploiter initially took a flash loan of 50,000 wstETH and 60,000 WETH from Aave and added 1,100 ETH to the steCRV pool in order to mint 1,023 steCRV.
Step 3:
Approximately 50,000 wstETH and 57,000 WETH were then added to the Balancer cB-stETH-STABLE pool in order to mint 109,517 B-stETH-STABLE.
Step 4:
The exploiter then deposited 1,000 steCRV and 233 cB-stETH-STABLE as collateral into Sturdy Finance to borrow 513 WETH.
Step 5:
This allowed them to manipulate the price of B-stETH-STABLE and set the steCRV token as non-collateral during the price manipulation.
Step 6:
The price of the B-stETH-STABLE increased by threefold; therefore, the protocol considered the earlier collateral of 233 B-stETH-STABLE enough to cover the debt position of 513 WETH, after which the set steCRV was no longer used as collateral.
Step 7:
The attacker then withdrew their collateral of 1,000 steCRV from Sturdy and then liquidated their position with 236 WETH to reclaim 233 B-stETH-STABLE for approximately 106 wstETH and 120 WETH.
Step 8:
The above steps were repeatedly executed with five different contracts, after which the exploiter repaid the borrowed amount of the flash loan to book their share of profit.
Step 9:
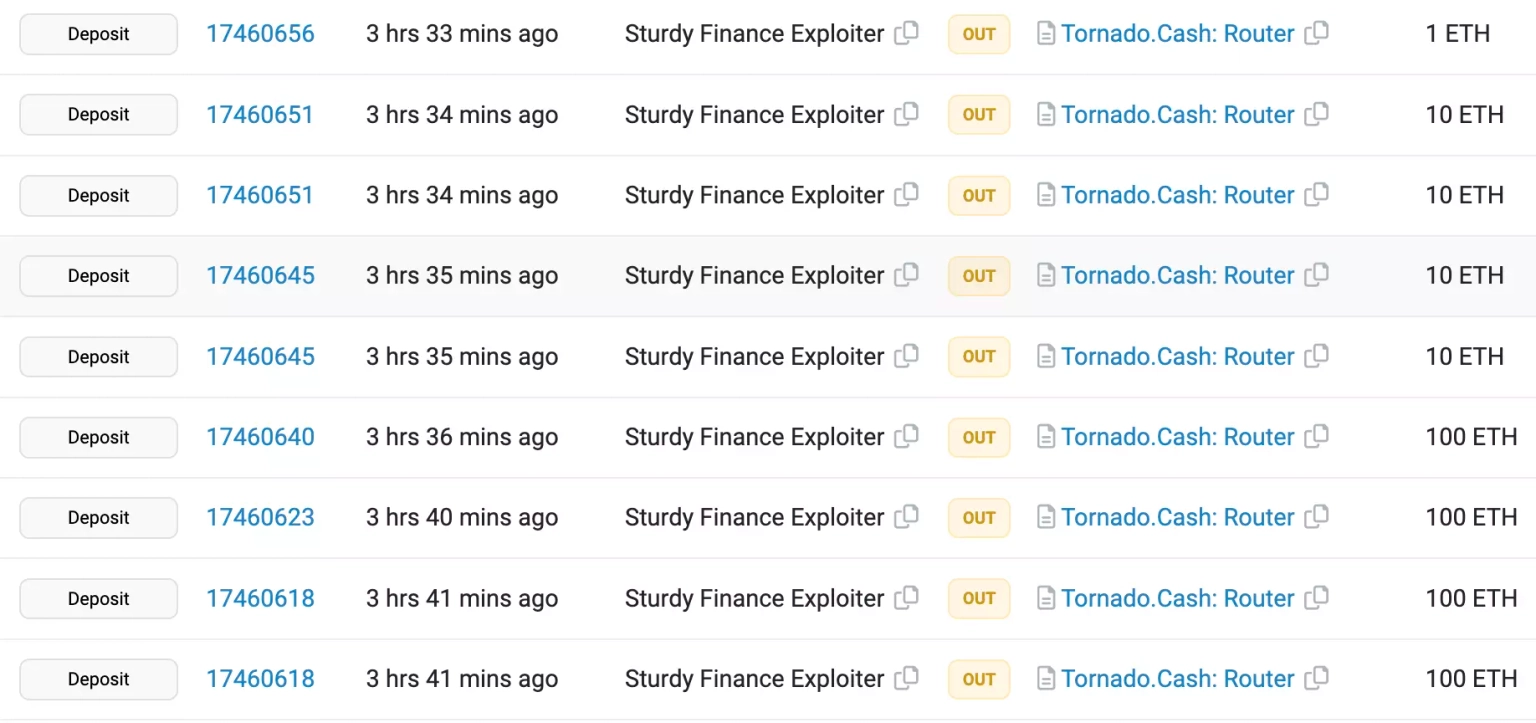
The exploiter has already transferred the stolen assets, worth 442.6 ETH, to Tornado Cash.
The team acknowledged the occurrence of the exploit and stated that all of their markets have been paused. No additional funds are at risk at the moment, and no user actions are necessary. The team is likely to share a detailed post-mortem of the exploit in the near future.
The field of smart contract development necessitates a rigorous approach to security, and part of that approach must encompass robust defensive measures such as reentrancy locks. The security of a project can be greatly enhanced by making these locks public, allowing developers to decide whether to revert the contract if the lock is engaged. Furthermore, reverting to view functions can be a valuable protective measure when the lock is active.
Regular audits of smart contracts by independent third-party auditors are another key element in safeguarding against attacks. These audits can identify potential vulnerabilities and provide recommendations for strategies to mitigate them, helping to prevent potential attack vectors from being exploited.
However, despite the most meticulous precautions, some attacks may still succeed. This is where solutions like Neptune Mutual can play a critical role in managing the aftermath of such incidents. If the Sturdy Finance team had established a dedicated cover pool with Neptune Mutual, the impact of this exploit could have been significantly curtailed. Neptune Mutual offers coverage for users who have suffered losses of funds or digital assets due to smart contract vulnerabilities, utilizing their innovative parametric policies.
When a user purchases a Neptune Mutual parametric cover policy, they do not need to provide evidence of their loss to receive payouts. Instead, once an incident has been confirmed and resolved through Neptune Mutual's incident resolution system, payouts can be claimed immediately. Presently, Neptune Mutual's marketplace operates on Ethereum and Arbitrum, two highly popular blockchain networks.
In addition, Neptune Mutual's security team would have assessed the Sturdy Finance platform for a range of potential vulnerabilities, including DNS and web-based security, frontend and backend security, and intrusion detection and prevention. These comprehensive evaluations can provide valuable insights into how a platform can further enhance its security.
Reference Source BlockSec