Analysis of the Curio Exploit
Learn how Curio was exploited, which resulted in a loss of approximately $16 million.
Youtube Video
Playing the video that you've selected below in an iframe

How was ORT token of the OMNI Real Estate project exploited due to smart contract vulnerability?
On January 17, 2023, the OMNI Real Estate project (ORT Token) on the BNB chain was attacked owing to a smart contract vulnerability, after which the hacker gained 236 BNB worth approximately $70,705.
Omni Group provides decentralized real estate market solution.
The root cause of the attack was the existence of a vulnerability in their StakingPool Contract, which did not have adequate parameter validation.
Step 1:
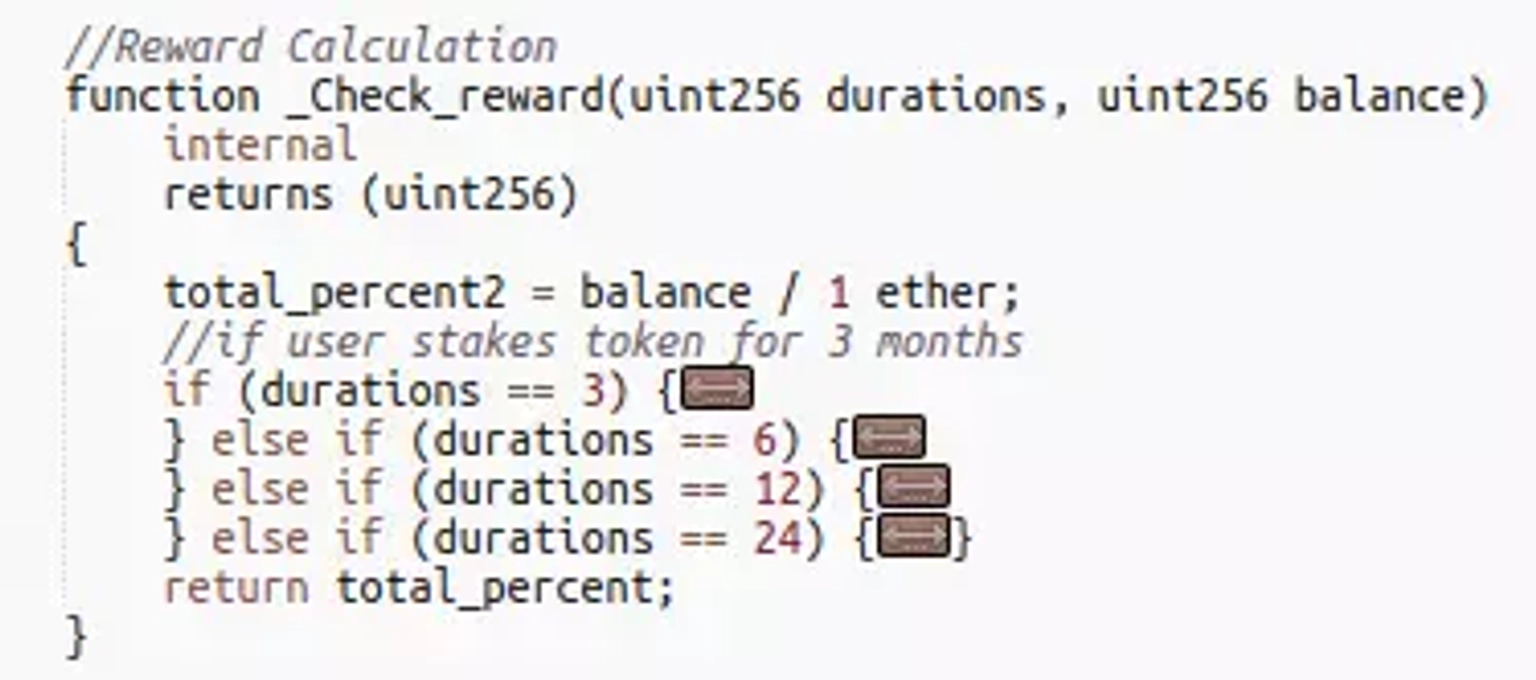
The reward is calculated by the contract using _Check_reward function, which has two parameters: durations, and balance.
Step 2:
The durations parameter is used to specify the time frame for a user stake period. When the durations value is 0, this method returns total_percent, a global variable, instead of performing the correct calculation.
Step 3:
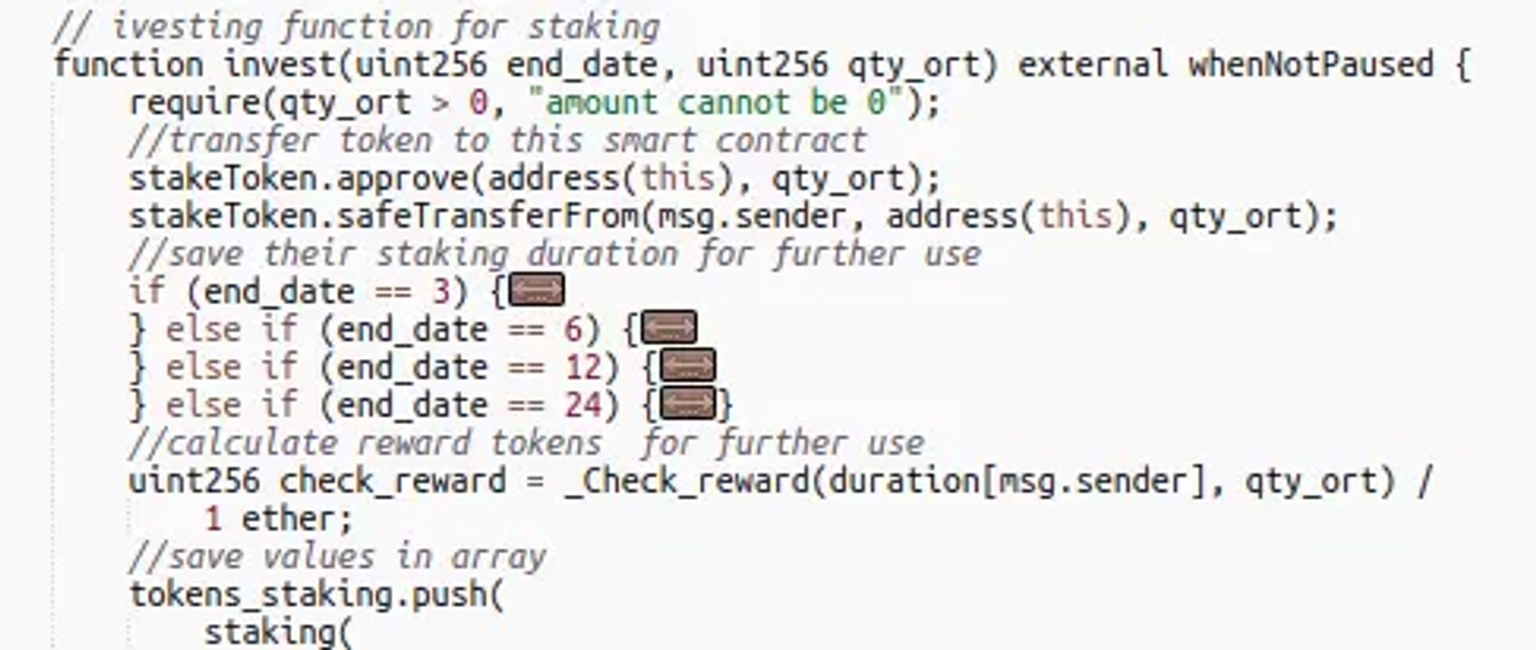
When the attacker called the invest function of the contract, the end_date value was set to 0, which effectively passed the contract’s verification. The durations parameter in the _Check_reward function takes value from this end_date parameter.
Step 4:
The exploiter deployed a couple of attack contracts to carry out his intended operations.
Step 5:
The attacker invested 1 Wei and then invoked the withdrawAndClaim function to withdraw ORT token rewards. These operations were repeated to earn profit.
Step 6:
The funding for the attack came from FixedFloat. The attacker later swapped the ORT tokens to BNB.
The team has not acknowledged the occurrence of the incident. However the price of their token has plummeted down drastically.

Omni Real Estate Token to USD Chart. Courtesy of CoinMarketCap
The attack's origin lay in a vulnerability residing within the StakingPool Contract, where inadequate parameter validation left a door open for exploitation. The _Check_reward function, responsible for calculating rewards, exhibited susceptibility when a particular parameter, durations, was set to 0. This deviation from the correct calculation allowed the attacker to circumvent the system's safeguards.
The hacker orchestrated a sequence of actions to exploit the vulnerability. By manipulating the duration parameter through cleverly timed invocations of the invest and withdrawAndClaim functions, the exploiter managed to amass rewards and extract profits through repetitive operations. The funding for this attack reportedly originated from FixedFloat, lending further complexity to the incident.
Curiously, the team behind the OMNI Real Estate project remained conspicuously silent in the aftermath of the attack, neglecting to acknowledge the occurrence of the breach. Unfortunately, this lack of response added to the uncertainty and highlighted the challenges users face when engaging with projects lacking transparency and accountability.
The preventive measures, however, are apparent. Implementing robust parameter validation mechanisms would have greatly mitigated the vulnerability, acting as a first line of defense against such attacks. By fortifying their smart contracts with thorough input validation, projects can ward off unauthorized access and manipulation.
Neptune Mutual, a beacon of security within the DeFi realm, offers a powerful solution to counteract the aftermath of such attacks. While we might not be able to forestall the occurrence of every hack, our dedicated cover pool in the Neptune Mutual marketplace could significantly alleviate the impact. Our parametric policies ensure that users who find themselves victims of smart contract vulnerabilities can claim payouts without exhaustive loss evidence once incidents are resolved through our governance system.
Furthermore, Neptune Mutual's comprehensive security evaluation ensures that platforms are fortified against potential threats. Collaborating with multiple partners for security audits guarantees a more thorough review of vulnerabilities, enhanced user asset protection, and a deeper understanding of a protocol's security posture.
Reference Source BlockSec