Analysis of the Curio Exploit
Learn how Curio was exploited, which resulted in a loss of approximately $16 million.
Youtube Video
Playing the video that you've selected below in an iframe

Learn how OlympusDAO suffered a loss of $300,000 due to a lack of input validation.
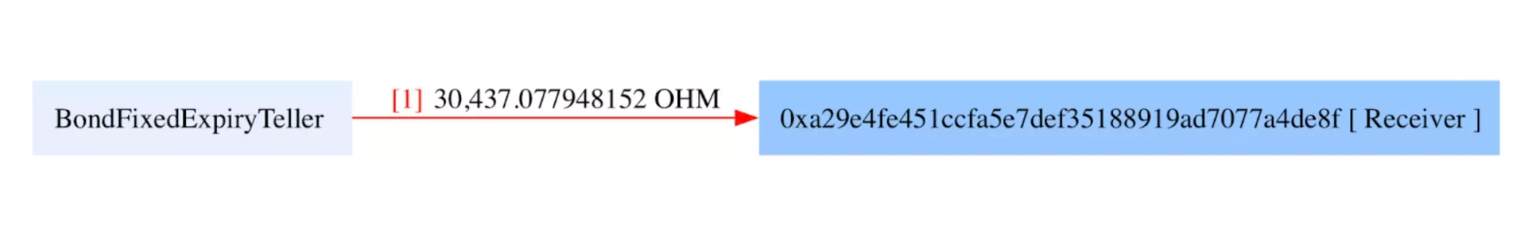
On October 21, 2022, OlympusDAO was exploited, resulting in a loss of 30,437 OHM tokens, worth approximately $300,000.
OHM, governed by the Olympus DAO, is a decentralized reserve currency, with the purpose of providing the Web3 financial ecosystem with a censorship-resistant currency that preserves purchasing power, has deep liquidity, is trusted, and is widely used as a unit of account.
The root cause of the vulnerability is due to a lack of input validation in the contract.
Step 1:
The DAO manages a token treasury in order to back the OHM token. The Treasury's goal is to ensure that the token maintains a certain floor price. If the token falls below that price, the treasury assets can be sold to purchase back OHM tokens, with the purpose of raising the token price back above that mark.
Step 2:
It employs a process called bonding in order to help the token stay above that threshold. The DAO purchases assets from investors for its treasury and issues OHM tokens to replace them. These bonds typically receive a 5-10% discount, and the tokens are distributed after a certain vesting period.
Step 3:
We attempted to analyze the attack transaction executed by the exploiter.
Step 4:
Inside the redeem function of the contract, it first checks to ensure that the token expiration of the requested token is at a later time than the current block. It then burns the amount of bonded tokens the user wants to redeem and transfers the underlying OHM token to the user.
/// @inheritdoc IBondFixedExpiryTeller
function redeem(ERC20BondToken token_, uint256 amount_) external override nonReentrant {
if (uint48(block.timestamp) < token_.expiry())
revert Teller_TokenNotMatured(token_.expiry());
token_.burn(msg.sender, amount_);
token_.underlying().transfer(msg.sender, amount_);
}Step 5:
However, there were no checks in place to ensure that the user's balance was greater than the amount of tokens being transferred. Additionally, there were no checks to ensure that the token passed was not malicious.
Step 6:
The attacker was able to create a malicious token contract and use that to request all of the available tokens in the contract.
It was later known that the affected contracts were not part of the OlympusDAO contracts. Instead, they were written by the Bond Protocol and used for the pilot launch of OHM bonds.
The team further stated that they will reimburse all of the users who were affected by this exploit. It was later found that the funds lost during the exploit were returned to the team.
We have created a proof of concept about the underlying hack using Foundry. The details surrounding the attack can be viewed in the GitHub gist.
The OlympusDAO hack was primarily a result of insufficient input validation checks in the contract. This lack of robust validation techniques, especially regarding user balances and potential malicious tokens, was the primary attack vector that the hacker exploited.
In order to mitigate such risks, comprehensive audits should be undertaken by multiple specialized blockchain security firms to ensure that all possible attack surfaces have been considered and secured. This involves a meticulous review of the code for vulnerabilities and conducting rigorous testing to identify potential security flaws.
Nevertheless, no system is perfectly secure, and it's in these situations that the invaluable role of protocols like Neptune Mutual is highlighted. If OlympusDAO had preemptively established a dedicated cover pool in the Neptune Mutual marketplace, the financial impact of the exploit on the affected users could have been substantially reduced.
Neptune Mutual provides parametric coverage policies, which enable users who suffer a loss of funds due to smart contract vulnerabilities to receive payouts without the need to provide explicit loss evidence. This swift compensation process helps to mitigate financial shocks and significantly speeds up the recovery process for users. At the moment, our marketplace is available on two popular blockchain networks: Ethereum and Arbitrum.
The Neptune Mutual security team could have helped assess OlympusDAO for DNS and web-based security, frontend and backend security, and intrusion detection and prevention. This additional layer of security evaluation could have potentially exposed the vulnerabilities before they were exploited.