Analysis of the Hedgey Finance Exploit
Learn how Hedgey Finance was exploited, resulting in a loss of assets worth $44.7 million.
Youtube Video
Playing the video that you've selected below in an iframe

FTX was targeted in a gas-stealing attack, resulting a loss of roughly corresponds to 81 ETH.
On October 13, 2022, FTX was the target of a gas-stealing attack, in which the hacker took advantage of the vulnerability by minting XEN tokens 17,000 times at zero cost. The amount of loss roughly corresponds to 81 ETH.
FTX is a centralized cryptocurrency exchange that specializes in derivatives and leveraged products. Its key product offerings include futures, leveraged tokens, options, MOVE contracts, and spot markets.
XEN is an ERC-20 token built on the Ethereum blockchain. It is founded on the fundamental principles of cryptocurrency, such as decentralization, self-custody, transparency, and trust through consensus. The XEN smart contract is immutable, lacks admin keys, and is open source.
The reason for this attack is that FTX does not limit the withdrawal transaction's gas limit while the withdrawal fee is free.
Step 1:
The attacker at first deploys the arbitrage contract and then performs an ETH withdrawal from FTX to the arbitrage contract.
Step 2:
The mint function of the XEN project is used in the fallback function of the arbitrage contract to acquire $XEN tokens.
Step 3:
The FTX exchange is the sender of the withdrawal transaction, thus the exchange itself will cover all gas costs.
Step 4:
FTX does not require the recipient to be the contract address, nor does it limit the amount on ETH gas.
Step 5:
A small amount of ETH will be transferred to the attack contract via the FTX hot wallet address, and subcontracts are created in batches.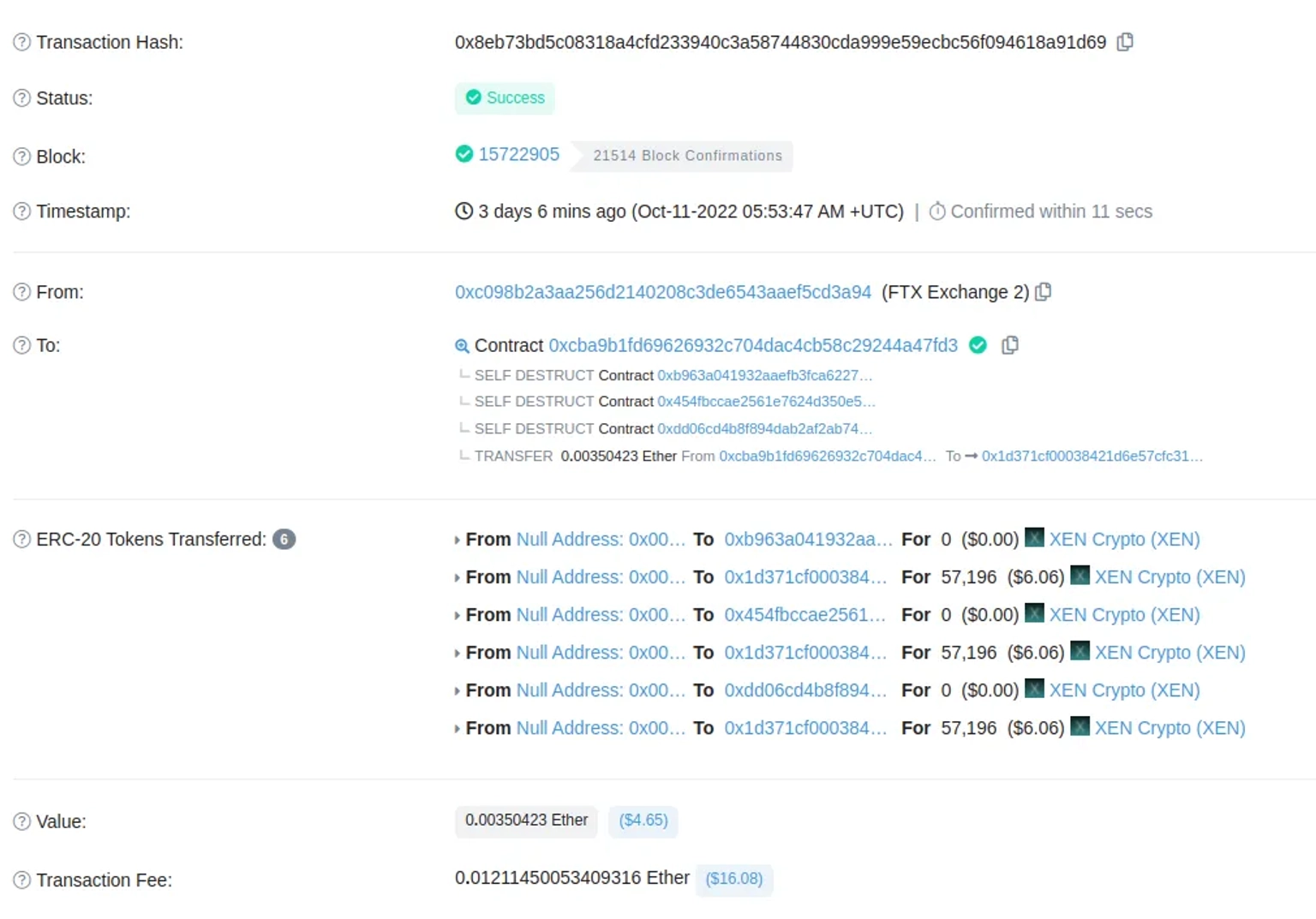
Step 6:
Each time the subcontracts are executed, they will self-destruct. The fallback() function of the subcontract will then initiate a mint request to the Xen contract.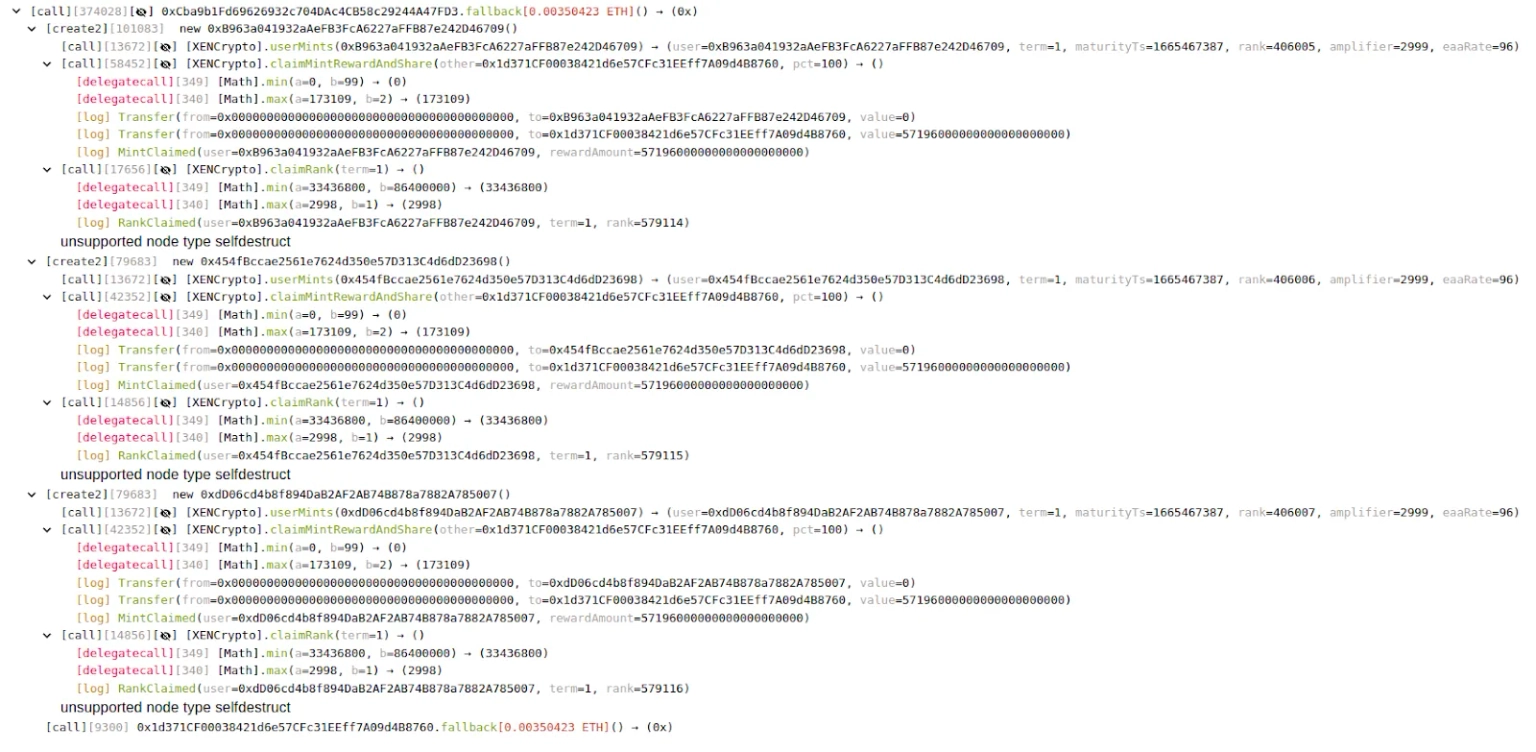
Step 7:
The claimRank() function simply requires the payment of the calling gas fee and passes in a term (>= 1 day) for minting.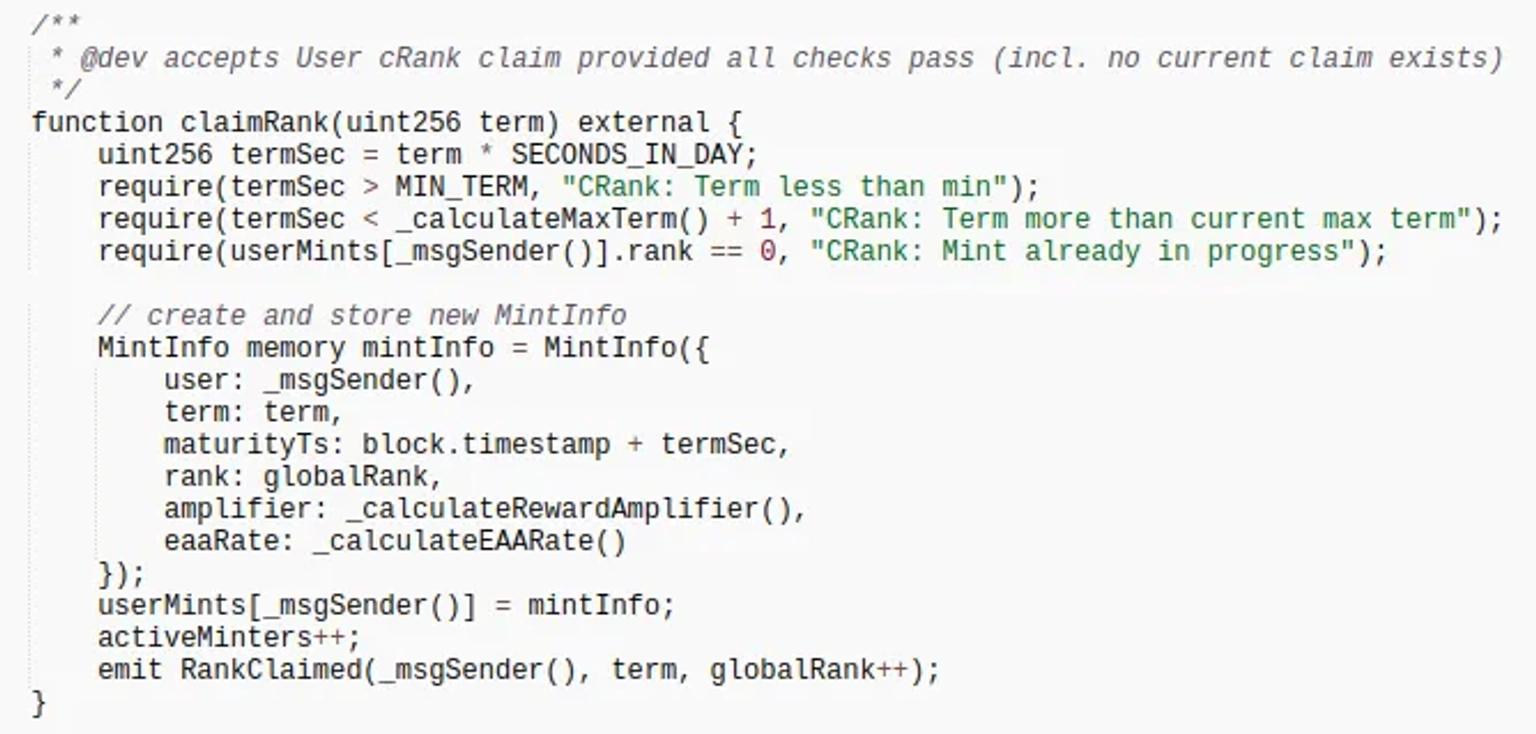
Step 8:
The claimMintRewardAndShare() function is used for claiming; it just determines whether the term has been met (1 day was set by the hacker), and then, it allows for unconditional withdrawal.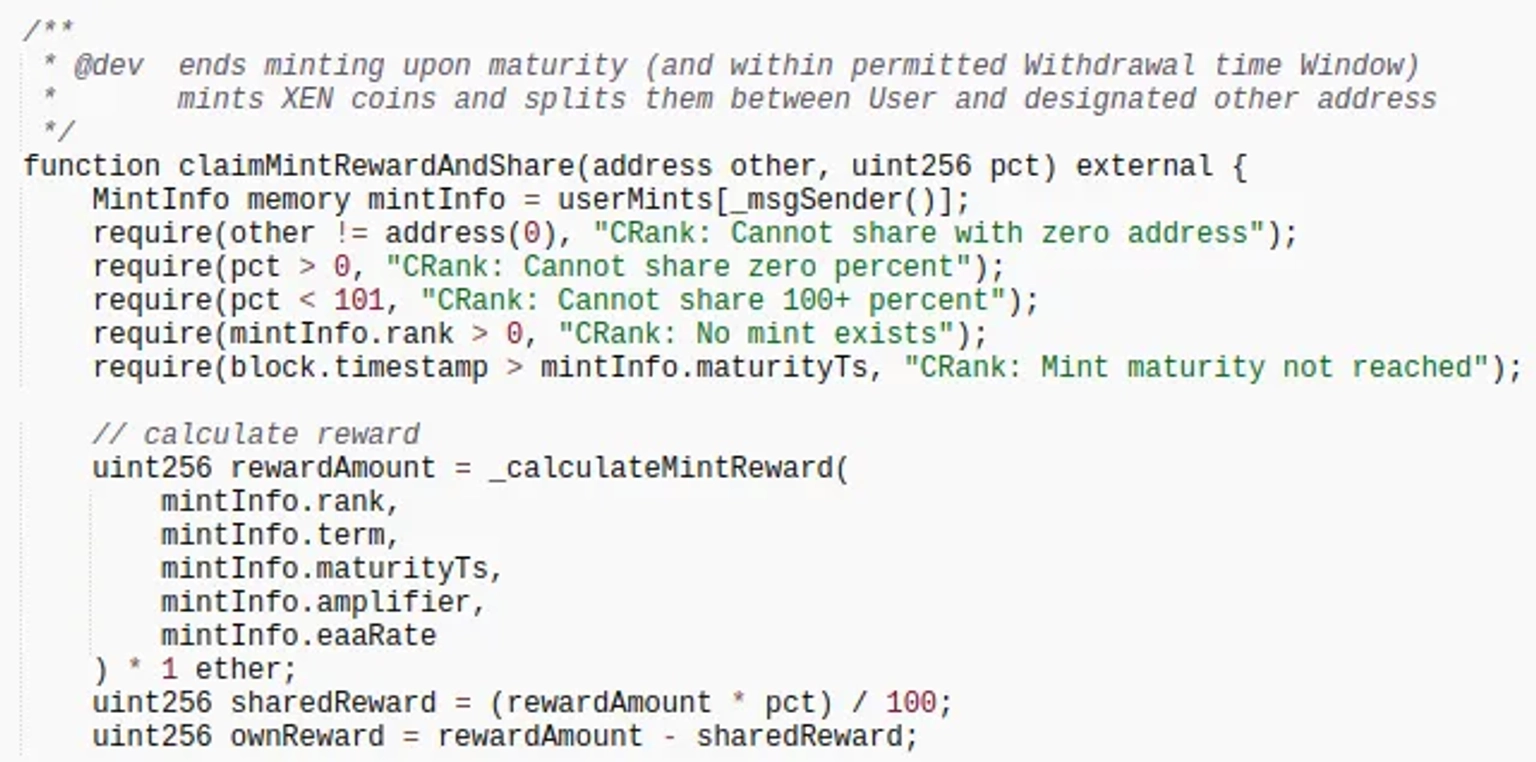
Step 9:
However, because the FTX hot wallet address is the transaction initiator in the calling process, the entire call process of gas is paid by the FTX hot wallet address, and the Xen mint address is the attacker's address.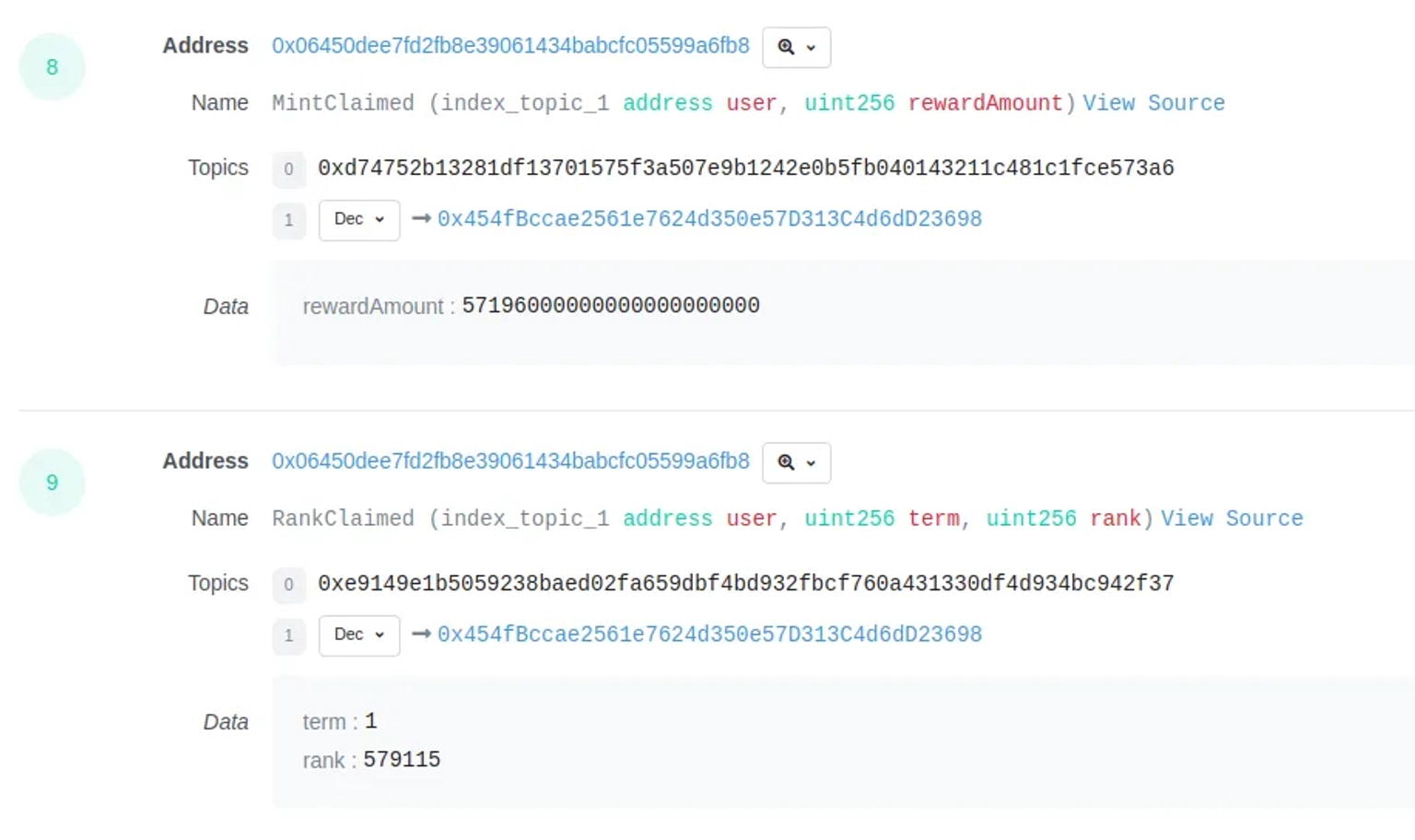
The XEN token's price has dropped by more than 33%. Through the loophole, the attacker has generated over 100 million XEN tokens. According to reports, the XEN token is also being targeted by a Sybil attack.
Anything that is practically quantifiable cannot be infinite. Gas limits could be set arbitrarily high, but this would have numerous consequences. The transaction size is bounded by the block size. As a result, specifying a gas limit greater than the block's gas limit is pointless.
Each block has a gas limit. A block gas limit has the advantage of preventing attackers from creating an infinite transaction loop. If a transaction's gas usage exceeds this limit, the transaction will fail.
Our security team at Neptune Mutual can validate your platform for DNS and web-based security, smart contract reviews, as well as frontend and backend security. We can offer you a solution to scan your platform and safeguard your protocol for known and unknown vulnerabilities that have the potential to have catastrophic long-term effects. Contact us on social media if you are serious about security and have the budget, desire, and feeling of responsibility to do so.